Security or policies may require that specific tasks be performed by different users. You can set up rules to separate tasks that must be performed by different users. This concept is named segregation of duties. This helps reduce the risk of fraud, and helps you detect errors or irregularities.
For example, you might not want the same person both to acknowledge the receipt of goods and to process payment to the vendor. Segregation of duties helps you reduce the risk of fraud, and it also helps you detect errors or irregularities. You can also use segregation of duties to enforce internal control policies.
To comply with regulatory requirements, such as those from Sarbanes-Oxley (SOX), International Financial Reporting Standards (IFRS), and the United States Food and Drug Administration (FDA), use segregation of duties.
Default duties are provided. The administrator can modify the privileges that are associated with a duty or create new duties.
The HR department of USMF has requested a rule for segregation of duties for the Access benefits workspace, and the Approve production journal. You must create the rule in Finance and Operations apps.
Complete the following procedure to create a rule. You must be a system administrator to complete the procedure. The demo data company used to create this procedure is DAT.
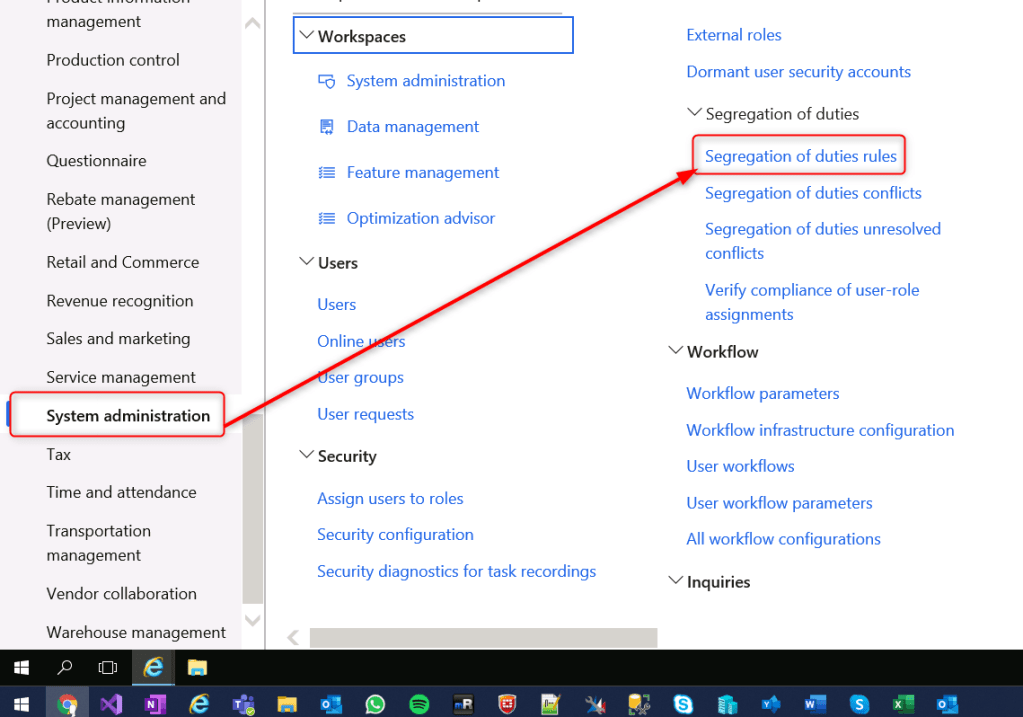
- Go to System administration > Security > Segregation of duties > Segregation of duties rules.
- Select New.
- In the Name field, enter a name for the rule.
- In the First duty field, select the drop-down button to open the lookup.
- In the list, find and select the first duty that is controlled by the rule.
- In the Second duty field, select the drop-down button to open the lookup.
- In the list, find and select the second duty that is controlled by the rule.
- In the Severity field, select the severity of the risk that occurs when the same user or role performs both duties.
- In the Security risk field, enter a description of the security risk.
- In the Security mitigation field, type a value.
- Enter a description of the actions that you take to mitigate the security risk.
- For example, you can mitigate the risk by conducting more detailed reviews of the process, by conducting a monthly managerial review, or by sharing resources with other departments.
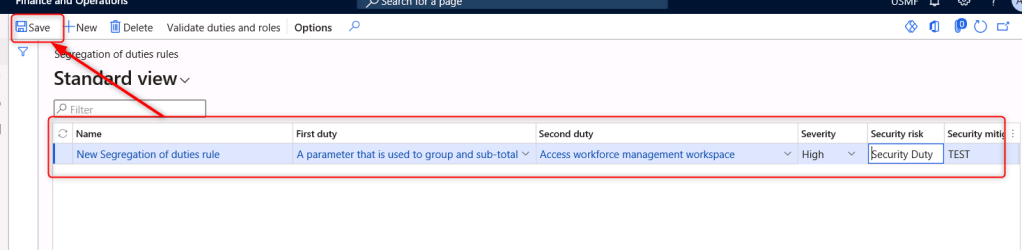
- Select Save.
- Close the page
Leave a comment