Reference article : https://docs.microsoft.com/it-it/learn/modules/role-security-finance-operations/
With role-based security, access to Finance and Operations apps is not granted to individual users, but to security roles to which users are assigned. A user who is assigned to a security role has access to the set of privileges that is associated with that role. If a user isn’t assigned to a role, they are unable to access the Finance and Operations apps application.
To access Finance and Operations apps and be assigned to a role, a user must have an authenticated Microsoft Azure Active Directory (Azure AD) account.
In Finance and Operations apps, role-based security is aligned with the structure of an organization. Users are assigned to security roles based on their daily job responsibilities. Depending on the user, one role or many roles might be assigned. Roles contain duties, privileges, and permissions that control access to system components. The administrator grants access to the user for the duties that they perform. After security roles, duties, and privileges have been set up, business managers can control user access as their business needs change.
Finance and Operations apps offers many duties, privileges, and permissions out of the box. If needed, you can create a new role, duty, privilege, or permission in Visual Studio.
While you can manage security roles in Finance and Operations apps, we recommend that you have a system administrator manage roles or modify duties and privileges behind the scenes in Visual Studio. Permissions can only be created or modified in the development environment. Each role has various duties assigned to it. A privilege can be directly assigned to a role, but it is best practice to assign a privilege to a duty. Within each privilege, various permissions are assigned. Permissions represent the most granular access to Finance and Operations apps.

Permissions represent access to individual securable objects, such as menu items and tables. Privileges are composed of permissions, and they represent tasks, such as generating a sales order. Privileges give the user access to perform a specific action. For example, one privilege might have read-only access to view a record, while another privilege grants access to create and edit a record.
Duties are composed of privileges and represent parts of a business process, such as maintaining vendor information. A single set of roles applies across all companies and organizations. An administrator no longer must create and maintain separate user groups for each company, as was the case in earlier versions. Even though roles are not specific to a company or organization, the administrator can control access by specifying a company or organization for a user in a role.
Example
An accounting example can help better explain duties, privileges, and permissions in the user interface of Finance and Operations apps.
In the accounting process cycle, there are the Maintain ledgers and Maintain bank transactions duties. The Maintain bank transactions duty contains the Generate deposit slips and Cancel payments privileges. The Cancel payments privilege contains permissions to the menu items, fields, and tables that are required to cancel payments. Each permission, privilege, and duty can be reused in other roles, duties, and privileges. For example, an Accounts payable manager would have the same permissions as an Accounts payable clerk, but would have additional managerial permissions as well.
Create new roles, duties, and privileges
In Visual Studio, you can create new roles, duties, and privileges by adding an item to your project in the Solution Explorer window. Additionally, you can create new permissions directly through a privilege in the element designer window.
Two ways to assign duties to a role are:
- Add a new duty within the Duties node of the role in the element designer window.
- Select a duty from the Application Object Tree (AOT) and drag it to the Duties node in the element designer window. This same process applies to assigning privileges to roles. You can also create an extension of an existing role, duty, or privilege. This would allow you to add or remove a duty from a role, or perhaps change a view-only privilege to an edit privilege for a certain page in Finance and Operations apps.
Follow these steps to create a new security element:
- In Visual Studio, go to the Solution Explorer window.
- Right-click your project and select Add > New Item.
- In the left column, under the Dynamics 365 Items node, select Security.
- Select Security Role, Security Duty, or Security Privilege, depending on the type of element that you need to create.
- Enter a Name for the security element.
- Select Add to add this element to your project. The element will now be open in the element designer window.
Enforce permissions policy
Permissions policies are used in role-based security to grant access to users for specific purposes. The most common type of security policy originates from a query that is stored in the AOT.
A query specifies the criteria that each row or record must satisfy to be returned by using the Ranges node in its data source. The Fields node specifies which fields should be returned. You can create a field security profile to use the permissions policies to restrict access to a certain field. After you create the profile, you can assign users or teams to that profile and then set up specific read, create, or write permissions for the field.
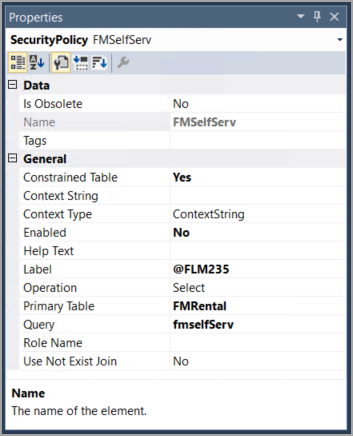
You can use permissions policies to ensure that users can view and access all necessary areas of Finance and Operations apps, from pages within the navigation pane to specific buttons on a page. A new security policy is added to a project through the Solution Explorer window by following the same steps as adding a new role, duty, or privilege to a project. In the Properties window, you can specify the details of the policy, such as the query that is the basis for the policy and the Primary Table, which is the first data source in the query that is assigned to the policy. Additionally, you can specify the Context Type, which is used to determine whether the policy is applicable.
The following image shows the Properties window of the RetailCustomer security policy that uses the RoleName context type. The Role Name property has been filled in to specify that the RetailStoreManager role is associated with this policy.

The following image is the Properties window of the FMSelfServ security policy that uses the ContextString context type. Notice that different fields are used as you select a different context type.
Extensible data security framework
To grant access to tables, fields, and rows in the Finance and Operations apps user interface, authorization is used. To restrict or deny access to those elements, you need to use data security. You can assign data security policies to security roles by using the extensible data security (XDS) framework.
XDS is an evolution of record-level security (RLS) that was available in Microsoft Dynamics AX 2012 and earlier versions. The XDS framework in Finance and Operations apps allows you and the administrators at your organization to help secure data in shared tables in such a way that users will have access to the part of the table that is allowed by the enforced policy. XDS policies are enforced, regardless of whether data is being accessed through the Finance and Operations apps cloud-based application, an SQL Server Reporting Services (SSRS) report, or other services.
The flow for an XDS policy is as follows:
- Start with a query to define the filters or limits that should be placed on the primary table or tables.
- Create a security policy that links to the query and primary table for which you want to restrict data access.
- Define the context for the rule. This could be based on a string, which would require additional development, or based on a role or group of roles.
- Define the list of constrained tables, which are related tables that store data from the primary tables for which you are attempting to restrict a subset of data.
Apply security permissions
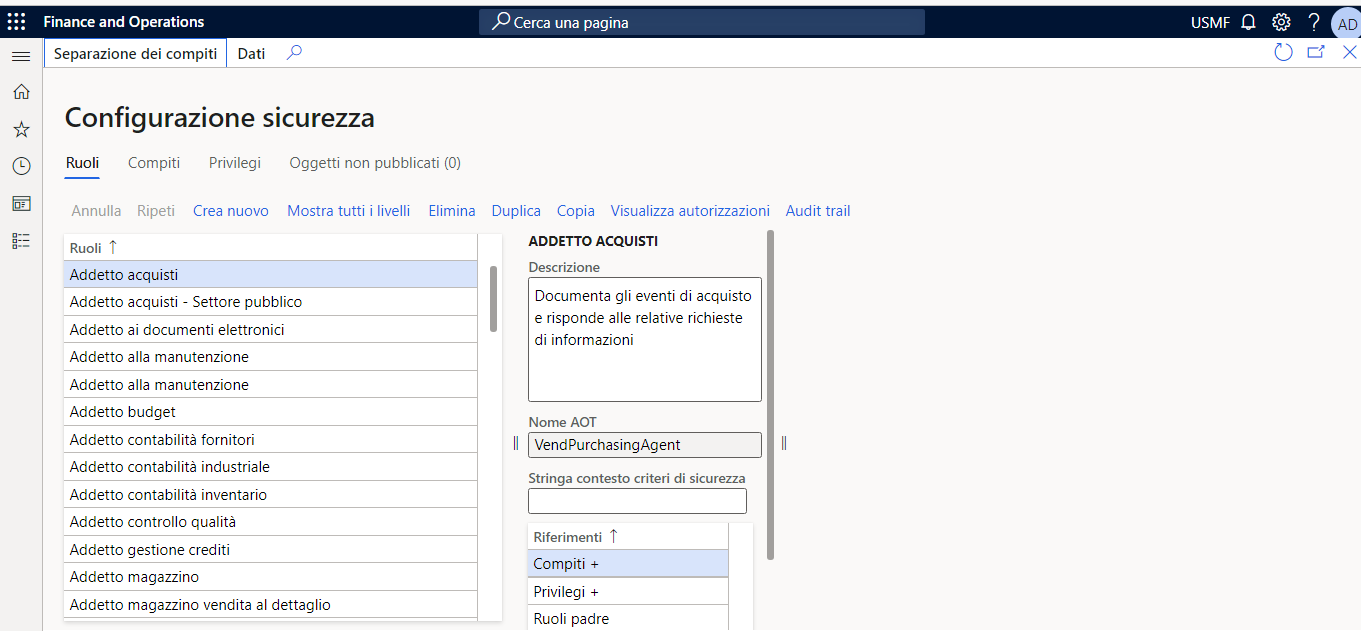
Users are assigned to security roles in the System administration module in Finance and Operations apps by going to Security administration > Security > Security configuration.
You can automatically assign users to roles by using queries from Visual Studio, or you can manually assign an individual user to a role. Additionally, you can choose to have a user excluded from automatic role assignment by resetting her or his status.
Follow these steps to assign users to roles automatically:
- In Finance and Operations apps, open the Navigation pane by selecting the menu icon in the top-left corner of the page.
- Under the Modules node, select System administration.
- Select Security to expand the node, and then select Assign users to roles.
- In the left column, select the role that you want to assign users to, such as Accounts payable clerk.
- In the middle column, beneath the Rules for dynamically assigning users to role heading, select Add rule.
- Select your desired query name for the rule, such as LedgerJournalPostControl.
- To modify the query, such as removing a company from the rule or adding a table join, select Edit query.
- In the Action Pane, select Run automatic role assignment. You will see the users that have been added in the middle column under the Users assigned to role heading.
Lab – Create a new security role and add duties
Scenario
The Finance and Operations apps developer has been asked by the Fleet Management company to create a new role based on a new position that they are filling for a Fleet Service Manager. The manager needs duties to manage cars and customers, as well as the basic duties that are associated with Fleet Management.
Create a new project
- Minimize the Internet Explorer window.
- Open Visual Studio.
- Select Yes in the Do you want to allow this app to make changes to your device? window.
- Open the File menu and select New > Project.
- In the New Project dialog box, ensure that Dynamics 365 is selected on the left pane under Templates.
- On the middle pane, select Finance Operations.
- Name the project FleetManagementSecurityProject.
- Select OK.
- Open the Dynamics 365 menu in the ribbon.
- Select Options.
- Under the Dynamics 365 node on the left pane, select Projects.
- Ensure the check boxes for Organize projects by element type and Synchronize database on build for newly created project are selected.
- Select OK.
Create the FMServiceManager role
- In the Solution Explorer window, right-click FleetManagementSecurityProject.
- Select Add > New Item.
- In the left column, under the Dynamics 365 Items node, select Security.
- In the middle column, select Security Role.
- Name the role FMServiceManager.
- Select Add to add the new security role to your project. The FMServiceManager role will now be open in the element designer window.
Add duties to the FMServiceManager role
- In the Application Explorer window, in the AOT, expand the Security node.
- Expand the Security Duties node.
- Select and drag the FMBasicDuties duty from the AOT in the Application Explorer window to the element designer window in the Duties node beneath the FMServiceManager role.
- Select and drag the FMManageCars duty from the AOT in the Application Explorer window to the element designer window in the Duties node beneath the FMServiceManager role.
- Select and drag the FMManageCustomers duty from the AOT in the Application Explorer window to the element designer window in the Duties node beneath the FMServiceManager role.
- Perform a build by right-clicking the project FleetManagementSecurityProject in the Solution Explorer window and selecting Build.
Leave a comment