This topic explains how to create a simple security policy that secures access to customers and customer groups, based on a range for a customer group.
Add a new query
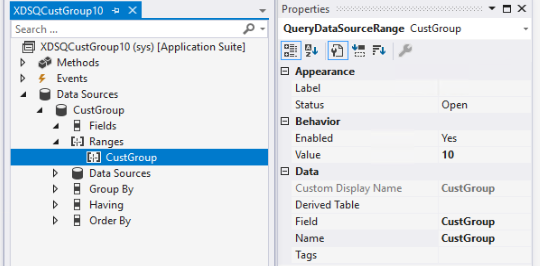
- In Visual Studio, add a new query, such as XDSQCustGroup10, to your project/solution. The query will be used to restrict data access from the Constraint table.

- Right-click Data Sources, and the select New Data Source.
- In the Table field, enter the primary table name CustGroup.
- Right-click Ranges, and then select New Range.
- Set the Enabled field to Yes.
- In the Data Source field, enter the primary table name, in this case, ‘CustGroup’.
- In the Value field, enter 10 to restrict access to data where CustGroup has value of 10, by defining the Range for the CustGroup field.
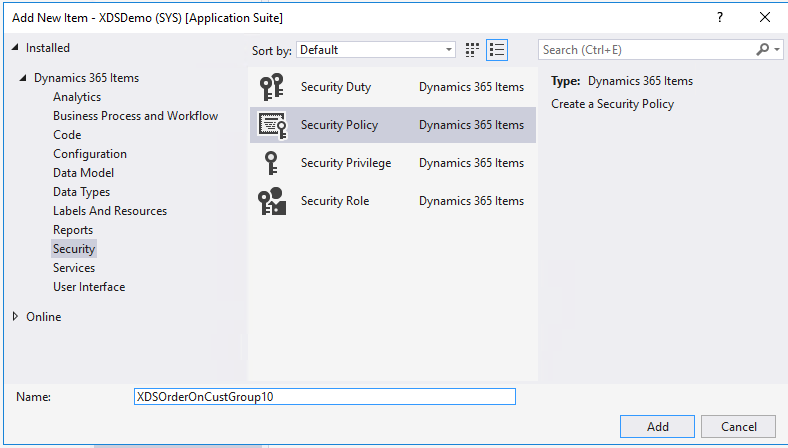
Add a new security policy
- Add a new security policy, such as XDSCustTableOnCustGroup10.
- Set Constrained Table to Yes. This will also secure access to the primary table. In this example this is the CustGroup table.
- Set the Context Type field to RoleName.
- Set the Enabled field to Yes.
- Set the Operation field to AllOperations. Other available values for Operation include Select, Insert, Update, Delete, and InsertUpdateDelete.
- Set Primary Table field to CustGroup.
- Set the Query field to the name of the query created above, for example ‘XDSQCustGroup10’.
- Set the Role Name field to ‘TradeSalesClerk’. Because Context Type is set to RoleName for this policy, it is required to enter the AOT name for a user role.
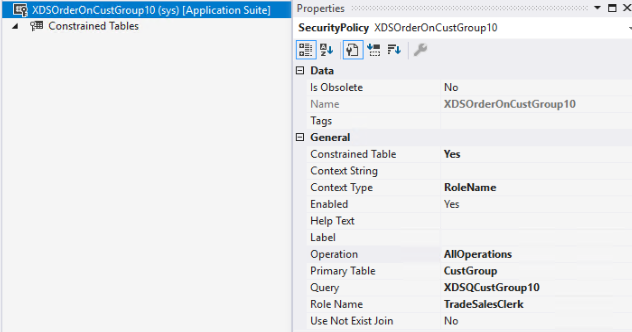
- Next, add constrained tables. In this simple example add one table.
 a. Right-click Constrained tables, and then select New > Constrained Table.b. Set Constrained to Yes.c. In the Name field, enter the Constrained table, for example ‘CustTable’.d. In the Table Relation field, enter the relationship to the primary table, in this case ‘CustGroup’.
a. Right-click Constrained tables, and then select New > Constrained Table.b. Set Constrained to Yes.c. In the Name field, enter the Constrained table, for example ‘CustTable’.d. In the Table Relation field, enter the relationship to the primary table, in this case ‘CustGroup’. - As a final step, it is required that you build and synchronize the solution to activate the policy.
Leave a comment